© 2025 EAMC – Managed. Secured. Assured. All rights reserved.
EAMC Knowledge Bank Publication Updates
Read More
Governments: SLED Technology ServicesNEW Service Offerings
EAMC Hosting
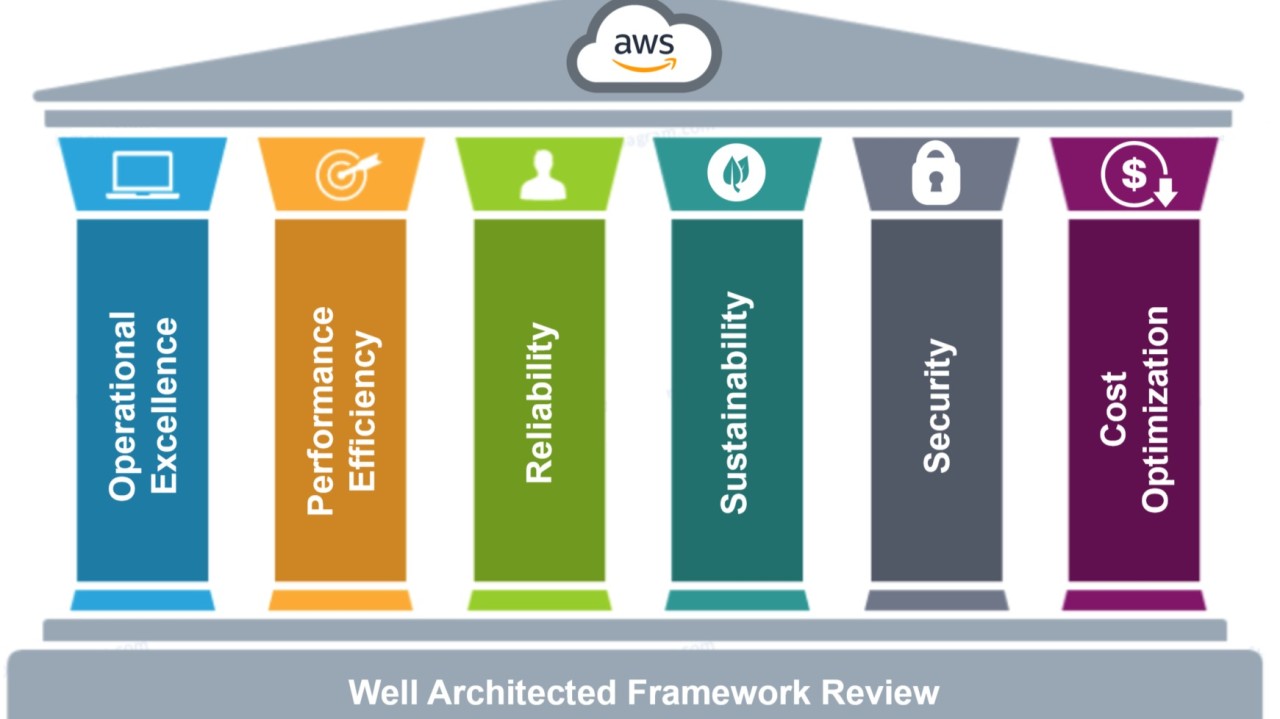
EAMhosting.com, a division of EAMC, delivers enterprise-grade web hosting solutions designed to support the evolving needs of government agencies, businesses, and nonprofit organizations. Our hosting platform combines performance, security, and reliability—empowering digital transformation through advanced infrastructure and around-the-clock support.
EAMhosting.com – Secure, Scalable, and Smart Hosting for the Modern Enterprise
Backed by EAMC's deep expertise in cybersecurity, cloud architecture, and compliance, EAMhosting.com offers scalable hosting services that meet stringent regulatory standards such as FedRAMP, FISMA, HIPAA, and CMMC. Whether you're launching a government portal, a secure cloud workspace, or a robust eCommerce environment, our platform ensures your data is protected and your mission stays online.
With tailored solutions for SLED (State, Local, and Education), federal contractors, and small to midsize businesses, EAMhosting.com is more than a hosting provider—it’s your trusted technology partner.
Power your digital presence with confidence. Host with eamhosting.com.