© 2025 EAMC – Managed. Secured. Assured. All rights reserved.
At EAMC, we help organizations lead confidently through complexity. As a trusted partner in digital transformation, cybersecurity, and enterprise architecture, we deliver governance-first solutions that ensure security, scalability, and sustainability — from infrastructure to innovation.
Our proprietary frameworks, including the EAMC Maturity Model™ and Cybersecurity as a Service (CSaaS) platform, are purpose-built for regulated industries navigating the risks and opportunities of cloud, AI, and next-gen technologies.
We don’t just respond to change — we anticipate it.
We don’t just deliver technology — we engineer assurance.
Whether you’re modernizing IT systems, aligning with regulatory frameworks, or preparing your enterprise for the future of AI, EAMC provides the clarity, control, and confidence needed to move forward — securely.
EAMC is about Clarity, Governance. Transformation with Security-first solutions for enterprise modernization.

In an era of increasing cyber threats, our on-premises solutions provide unparalleled protection for sensitive data and critical infrastructure.

EAMC enables seamless adoption of cloud solutions, empowering organizations to scale operations, enhance agility, and optimize costs.

Harnessing the power of AI, EAMC delivers intelligent solutions that drive innovation and efficiency

Our focus on quantum applications ensures our clients benefit from cutting-edge advancements in cryptography.
EAMC offers comprehensive management services tailored to enhance operational efficiency and drive measurable outcomes.
EAMC is a trusted leader in delivering cutting-edge solutions in On-Premises Cyber Security, Cloud Computing, Artificial Intelligence (AI), Quantum Computing, Management Services, Managed Services, and Governance, Risk & Compliance (GRC) management. With over 20 years of experience serving the U.S. Federal Government and Department of Defense, we combine technical expertise with a deep understanding of the unique challenges faced by public and private sector organizations.
In an era of increasing cyber threats, our on-premises solutions provide unparalleled protection for sensitive data and critical infrastructure. EAMC specializes in deploying advanced security frameworks, leveraging state-of-the-art tools for threat detection, prevention, and response. By safeguarding your internal networks, we help ensure your organization maintains operational continuity and compliance with stringent security standards.
EAMC enables seamless adoption of cloud solutions, empowering organizations to scale operations, enhance agility, and optimize costs. Our expertise spans cloud migration, hybrid cloud architectures, and secure cloud environments, ensuring robust and compliant solutions for mission-critical workloads.
Harnessing the power of AI, EAMC delivers intelligent solutions that drive innovation and efficiency. From predictive analytics to automation, our AI capabilities enable clients to gain actionable insights, streamline operations, and stay ahead in a competitive landscape.
EAMC is at the forefront of emerging technologies, leveraging quantum computing to tackle complex problems with unprecedented speed and accuracy. Our focus on quantum applications ensures our clients benefit from cutting-edge advancements in cryptography.
EAMC offers comprehensive management services tailored to enhance operational efficiency and drive measurable outcomes. From strategic planning to process optimization, our team employs innovative methodologies and technologies to deliver solutions that empower organizations to achieve their goals. Whether improving resource allocation or implementing scalable management frameworks, EAMC ensures tangible results for our clients.
Navigating complex regulatory environments can be challenging, but EAMC simplifies the process through robust GRC solutions. We integrate governance strategies, risk mitigation protocols, and compliance measures into a cohesive framework, enabling organizations to minimize vulnerabilities and maintain accountability. Our approach not only reduces risk exposure but also strengthens trust with stakeholders.
EAMC offers comprehensive management services tailored to enhance operational efficiency and drive measurable outcomes. From strategic planning to process optimization, our team employs innovative methodologies and technologies to deliver solutions that empower organizations to achieve their goals. Whether improving resource allocation or implementing scalable management frameworks, EAMC ensures tangible results for our clients.
At EAMC, we believe that cybersecurity is not just a service-it’s a responsibility. That’s why we established the EAMC Cyber School, a workforce development initiative focused on educating and empowering individuals from underserved communities with the skills needed to thrive in today’s digital economy.
EAMC Cyber School provides hands-on training in cybersecurity, data analytics, and cloud technologies, helping close the opportunity gap while preparing the next generation of cyber defenders. With a curriculum grounded in real-world enterprise architecture and federal compliance frameworks, we equip students to succeed in both public and private sector careers.
In today’s rapidly evolving digital landscape, staying ahead requires access to the right information at the right time. EAMC’s KB is your gateway to expert-driven insights, compliance regulations, and cutting-edge research in Enterprise Architecture, Cybersecurity, Governance, Risk & Compliance (GRC), and Emerging Technologies.
info@eamsecured.com
(866) 953-4111
120 watefront St – Suite # 420 National Harbor, MD 20745

Stay ahead of the curve!—follow and subscribe to our social media channels below to remain digitally engaged.
Maryland (MD) MBE/WBE/ACDBE/ SBE/DBE/SBR/ # 23-293



MD TEDCO #T031304062412
MD IT Reseller #19674498
Virgina (NOVA) –


GSA Schedule 70 –
© 2025 EAMC – Managed. Secured. Assured. All rights reserved.
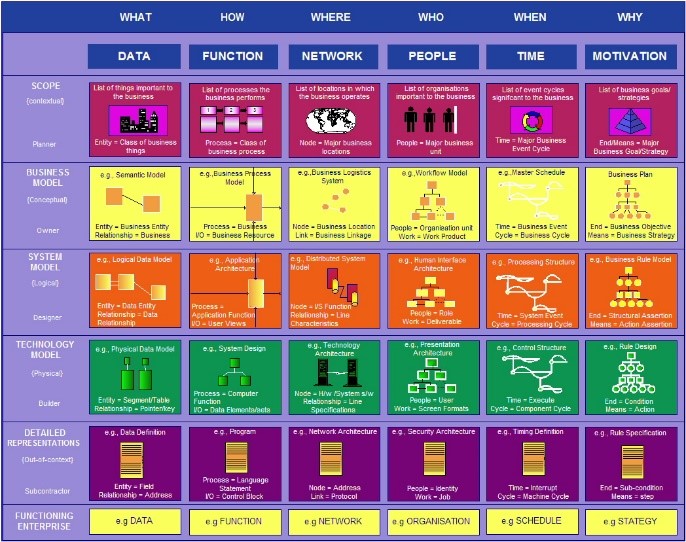
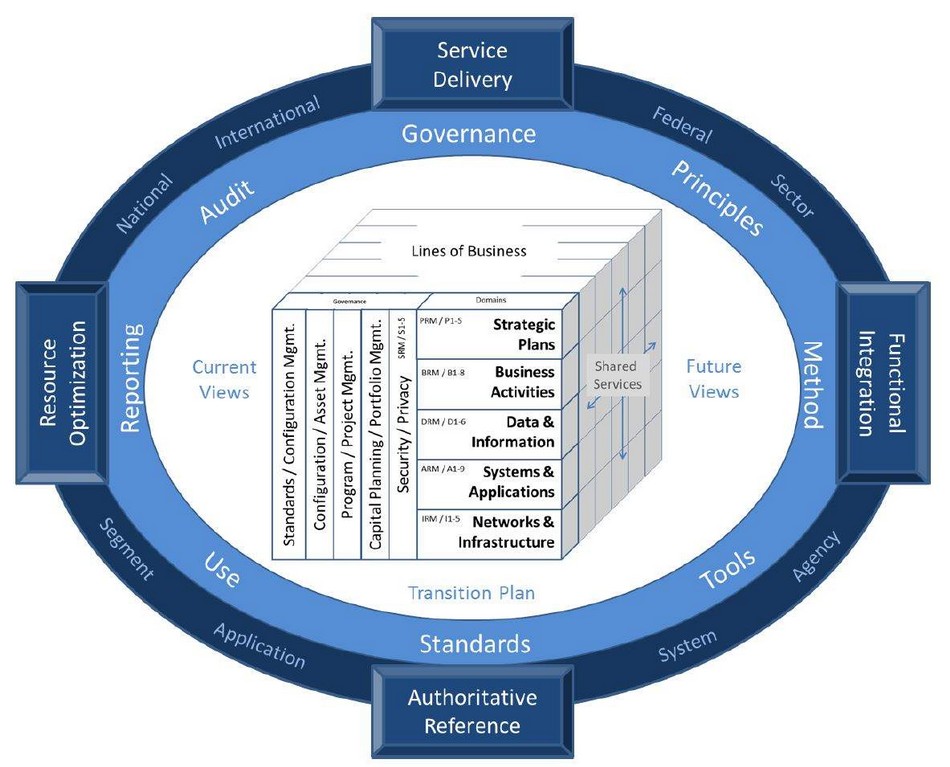
The Zachman Framework organizes enterprise architecture using a Two-Dimensional Classification Schema, with six interrogatives (What, How, When, Who, Where, Why) in a 6x6 Matrix Structure. It serves as an Enterprise Ontology, defining essential components, but is Not a Methodology, focusing on structuring architectural artifacts rather than guiding implementations.
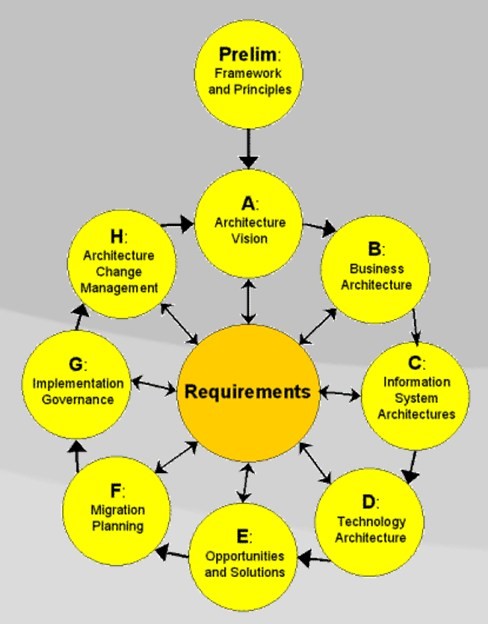
TOGAF (The Open Group Architecture Framework) is a globally recognized enterprise architecture credential. It provides a structured approach to designing, planning, implementing, and governing IT architecture. TOGAF follows a high-level design approach, modeled at four levels: Business, Application, Data, and Technology, emphasizing modularization, standardization, and leveraging proven technologies and products.
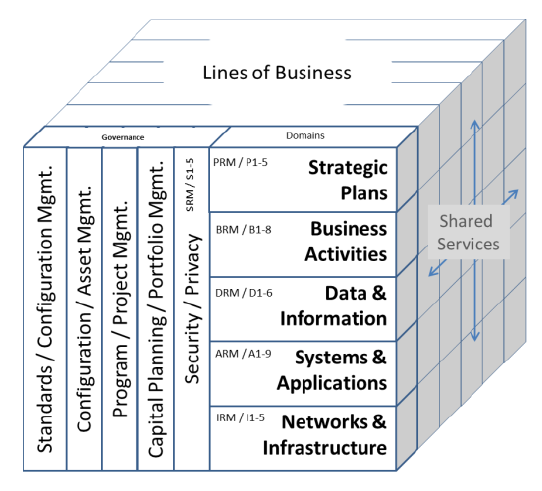
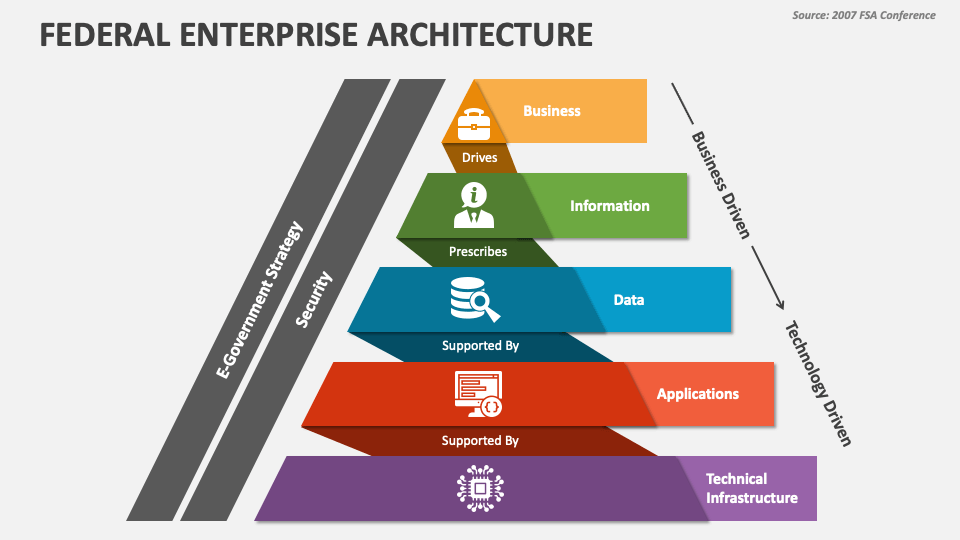
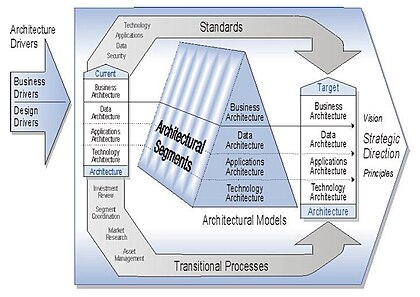
Enterprise architecture consists of four key components: Business Architecture, defining roles, processes, and objectives; Data Architecture, managing the information used for operations; Application Architecture, overseeing software applications processing data; and Technology Architecture, supporting all layers with hardware and communication technology. Together, these components ensure efficient, structured, and scalable business operations.
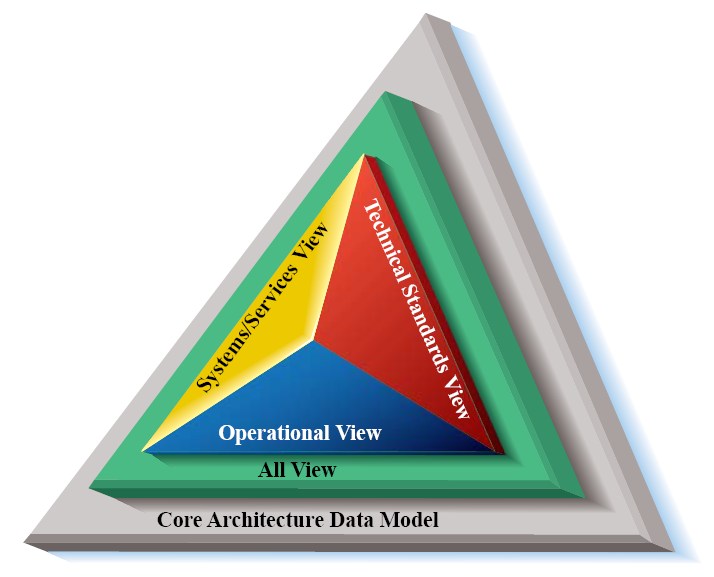
The Department of Defense Architecture Framework (DODAF) is a comprehensive framework used by the U.S. DoD to develop and manage enterprise architectures. It provides a structured approach for representing and visualizing DoD systems, ensuring all stakeholders have a clear, consistent understanding of system structure and behavior for effective decision-making and operations.
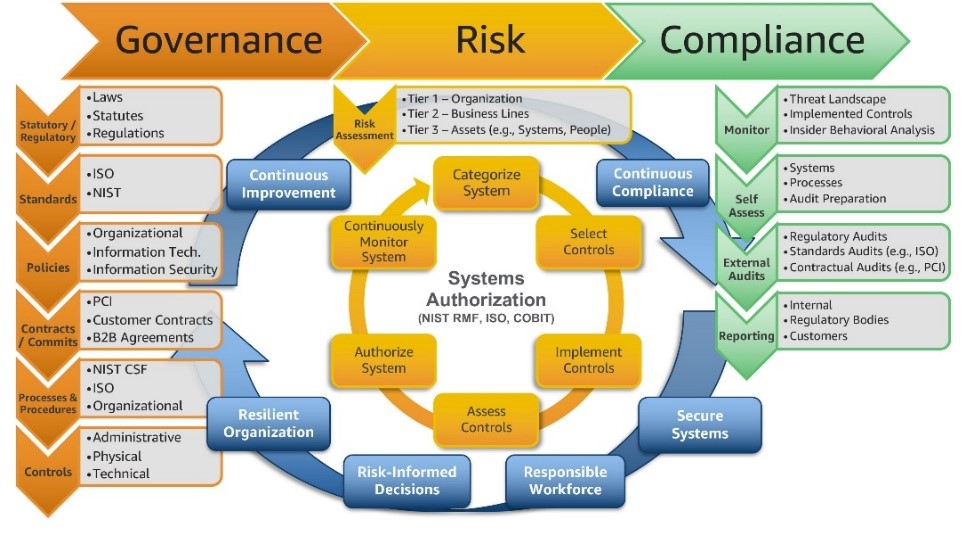
Governance, Risk, and Compliance (GRC) is a structured approach aligning IT and business goals while managing risks and meeting regulations. Governance sets policies and accountability, risk management identifies and mitigates threats, and compliance ensures adherence to laws. Integrating these enhances decision-making, efficiency, and business continuity while minimizing risks and regulatory issues.

The Risk Management Framework (RMF) integrates security, privacy, and cyber supply chain risk management into the system development life cycle. It follows a risk-based approach to control selection, considering legal, policy, and regulatory constraints. RMF applies to new and legacy systems across all technologies and organizations, ensuring effective information security and privacy management.
Enter your content here. This area supports rich text formatting.
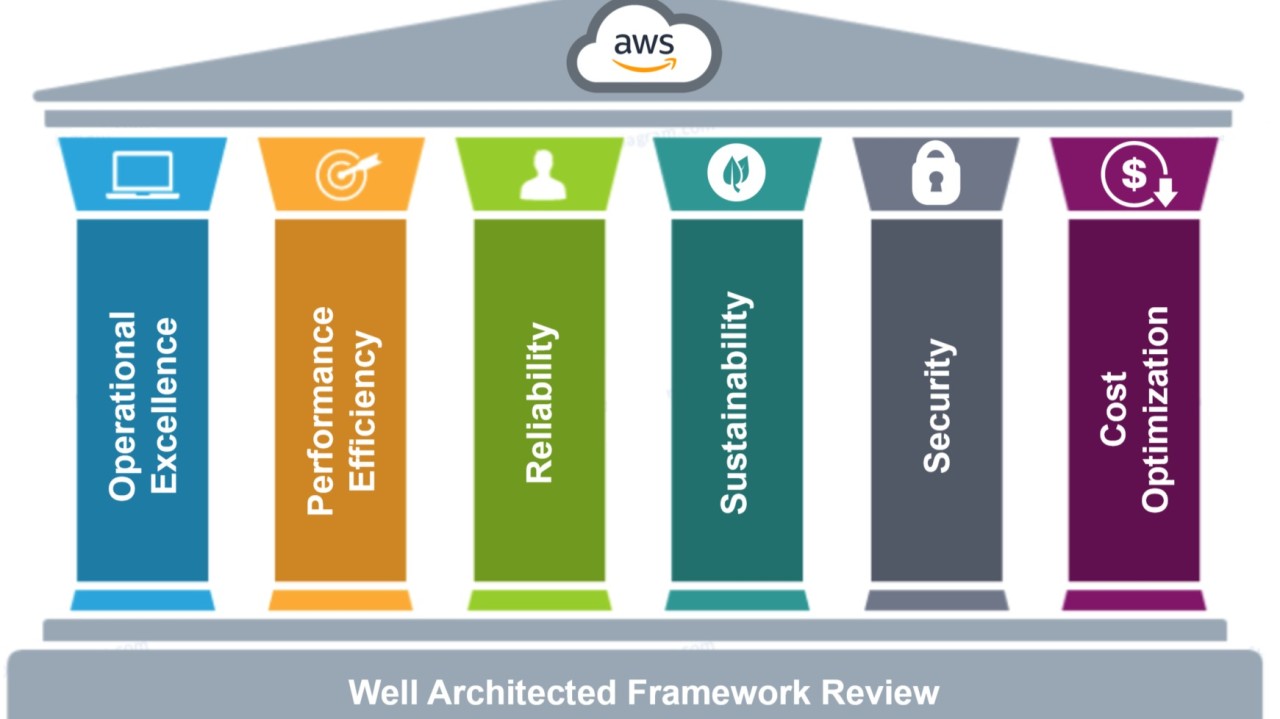
The AWS Well-Architected Framework helps assess whether a specific architecture aligns with cloud best practices. It provides a consistent approach to evaluating systems based on modern cloud standards and identifies necessary improvements. As AWS evolves, the framework is continually refined to incorporate learnings from customer experiences and advancements in cloud technology.
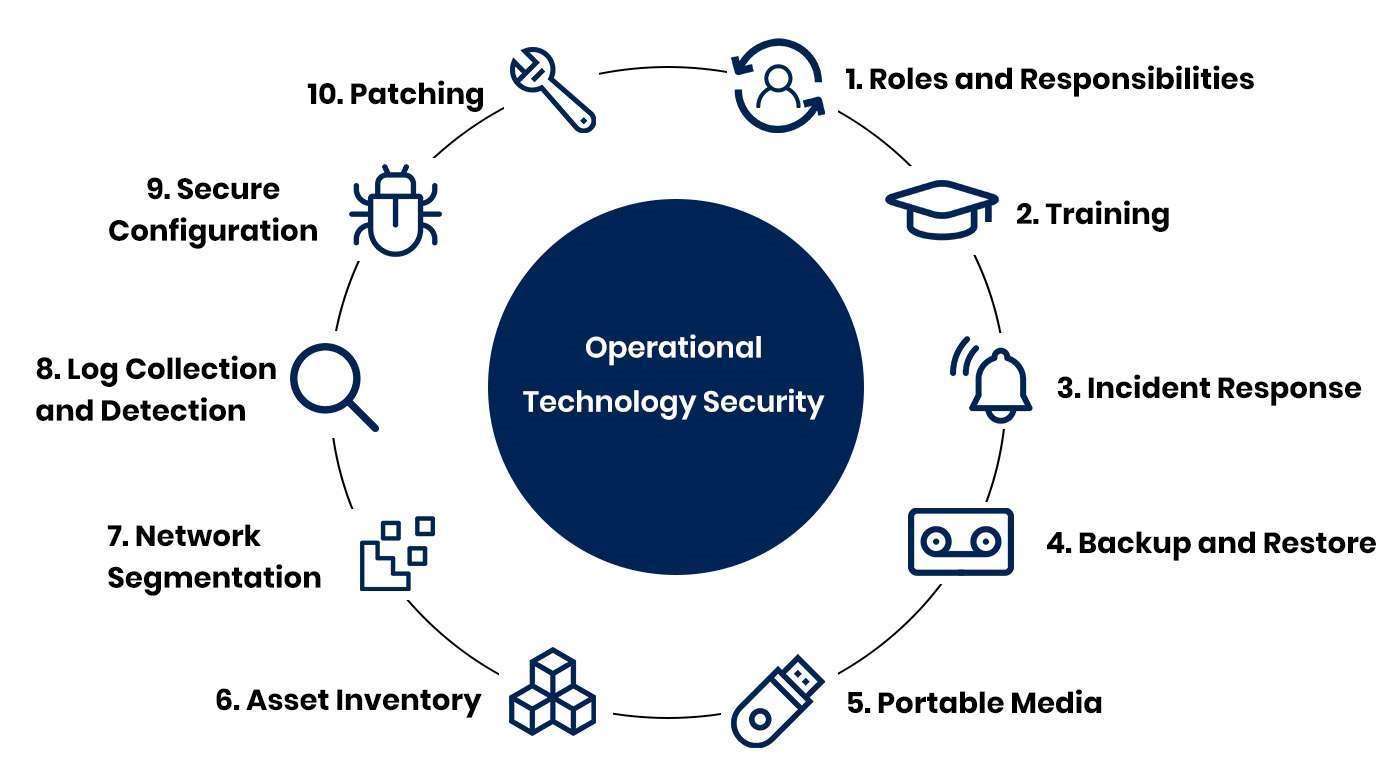
Operational Technology (OT) cybersecurity focuses on protecting the hardware and software that manage and control physical devices and processes in industrial environments.
Key aspects of OT cybersecurity include:
Transform data into actionable insights with advanced analytics and data governance solutions that drive informed decision-making.
An enterprise data architecture framework (EDAF) is a structured approach to managing and organizing data within an organization. It encompasses the entire data lifecycle, from collection and storage to processing and analysis.
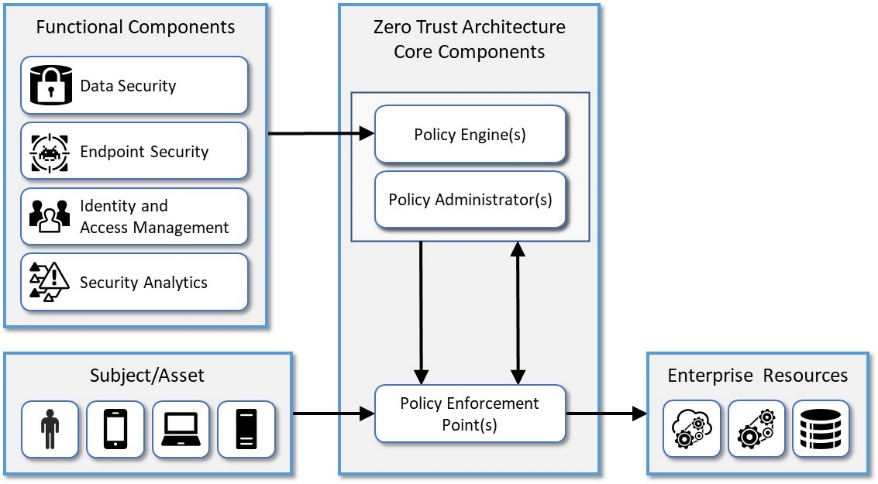
The NIST Zero Trust Architecture (ZTA) is a cybersecurity framework that emphasizes the principle of "never trust, always verify." It focuses on securing resources, users, and assets by assuming no implicit trust based on network location or ownership. You can explore the official NIST publication on Zero Trust Architecture here. Additionally, you might find a detailed guide and diagram in the NIST Special Publication 800-207.
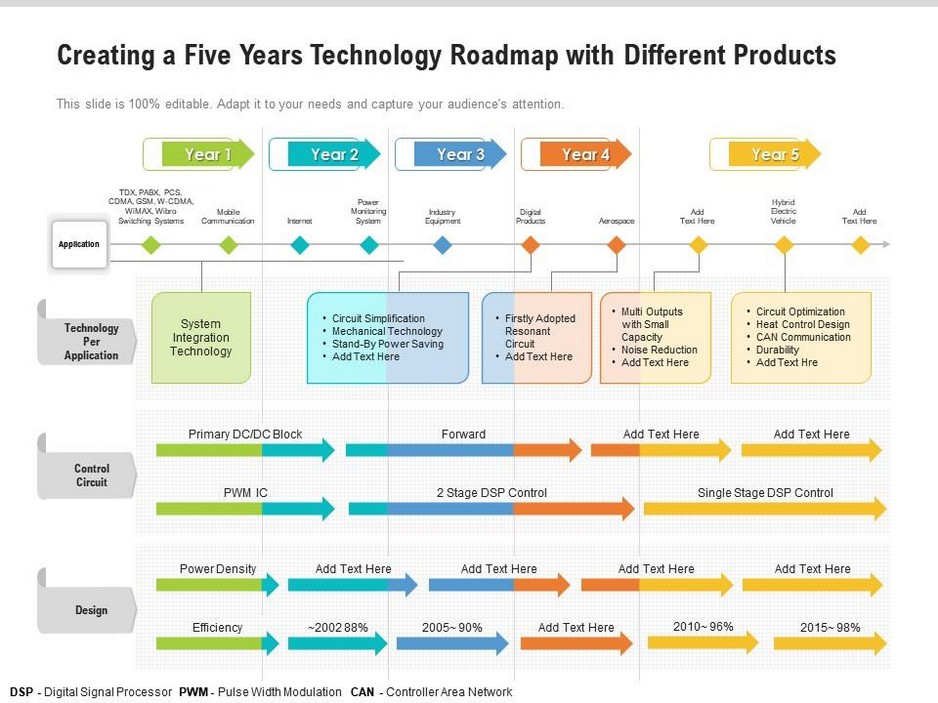
A Technology Roadmap is a strategic plan that outlines the technology initiatives an organization plans to undertake over a specific timeframe. It helps align technology projects with business goals, ensuring that all stakeholders understand the “what”, “why”, and “when” of IT initiatives.
Here are some key benefits of a Technology Roadmap:
The Modernizing Government Technology (MGT) Act is a new federal act that mandates federal agencies to accelerate their IT modernization efforts. The act allows agencies to reprogram unused budget allocation to fund future IT modernization projects. It also updates the uses of the Technology Modernization Fund (TMF) to pay for retiring and replacing older information technology (IT) systems.
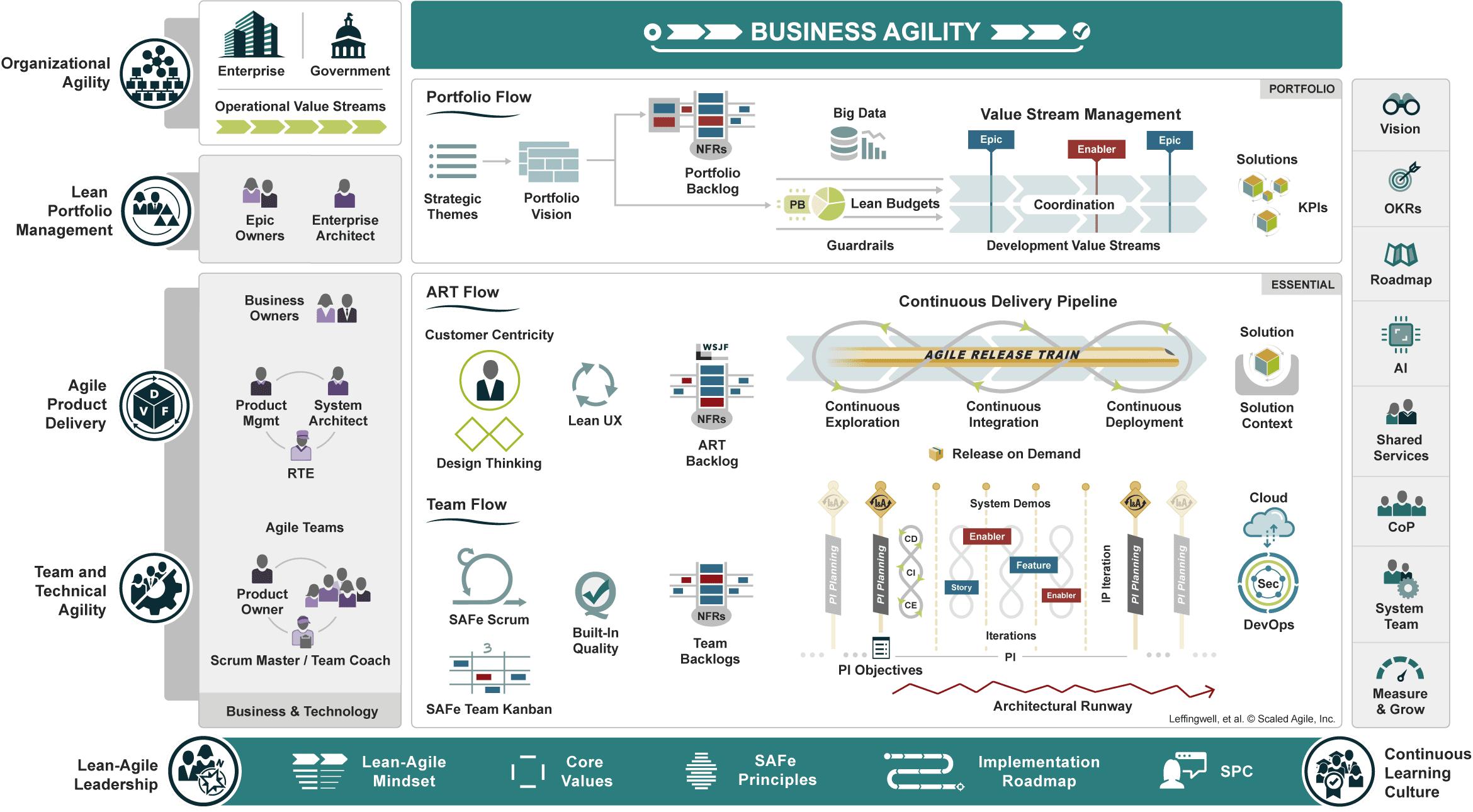
Product vision – Describes the desired future state of the product and guides Agile ARTs and teams toward a common goal.
Product strategy – Defines how the organization will deliver against the product vision, providing clear direction while retaining the agility needed to evolve based on feedback and market conditions.
Product design – Combines customer centricity, design thinking, and lean user experience (lean UX) design to understand the problem to be solved deeply and discover solutions with the best product-market fit.
Product delivery – Accelerates value realization by ensuring that new ideas flow quickly from idea to impact through a Continuous Delivery Pipeline.
Product marketing – Raises awareness and excitement in the market by amplifying the features and benefits of product innovations.
Product innovation culture – Fosters continuous learning, experimentation, and a spirit of relentless improvement across the organization.
© Scaled Agile, Inc.
The Modernizing Government Technology Act reforms and reauthorizes the Technology Modernization Fund (TMF) and its governing board, the Technology Modernization Board (TMB), which were established by the bipartisan Modernizing Government Technology Act of 2017 (P.L. 115-91). The bill includes several measures to improve the administration of the TMF and ensure program operations adhere to original congressional intent. The bill requires TMF awards to be reimbursed at the level needed to ensure the Fund is operational and creates a new requirement that agency’s reimburse administrative fees. The bill also establishes a Federal Legacy IT Inventory, a new oversight tool that will allow Congress to evaluate agency and government-wide priority items for legacy IT modernization and to assess how well the TMF does in funding these projects. Finally, this bill reauthorizes the TMF and TMB and establishes a December 2031 sunset.

FISMA compliance refers to adhering to a set of policies, standards, and guidelines to protect government information and systems. It is mandatory for federal agencies and their contractors. The key steps to achieve FISMA compliance include: